How to Prepare for a Potential Ransomware Attack?
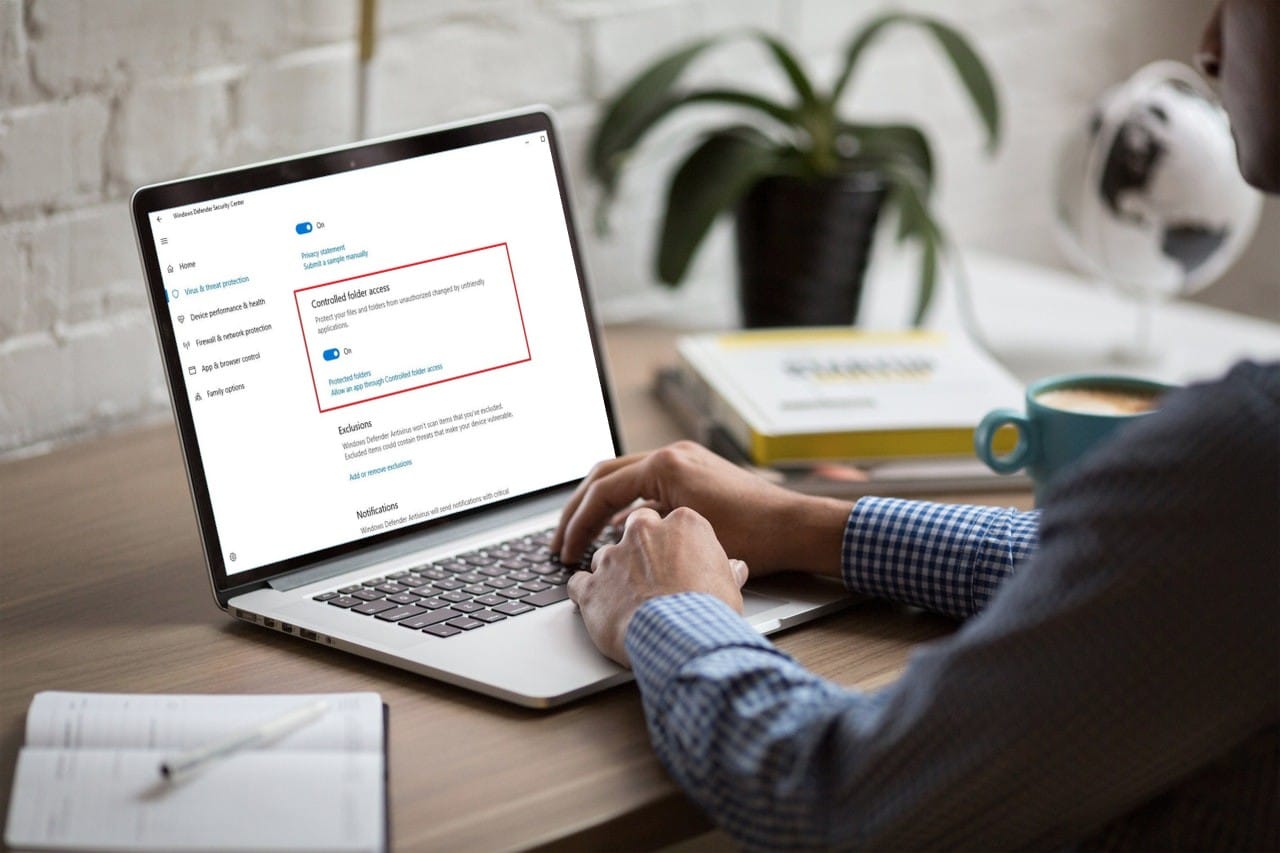
With the growth of technology, it is no news that viruses and malware can attack anyone. But, of course, everyone is aware that not all viruses are equally harmful. In today’s article, we will look at a particular virus called the ransomware virus. What is ransomware? Ransomware is a virus, malicious software that can take […] More